How & Why Social Engineering Works
Key points:
- Social engineering plays a major role in orchestrating 98% of cyberattacks
- The human factor is the weakest link that makes social engineering possible
- Educating potential targets is key to battling social engineering tactics
- With strong cybersecurity measures, it’s possible to render social engineering methods useless
Did you know that 98% of all cyberattacks involve some form of social engineering? Social engineering is a term that cybersecurity experts use to define a wide range of malicious activities that become successful due to human interactions.
Malicious actors use psychological manipulations to trick users into making errors, sharing sensitive information, clicking wrong links, downloading dangerous files, and more.
Social engineering attacks usually have several steps, including investigating the victim’s weaknesses and evaluating potential entry points. Using the gathered information, attackers gain the victim’s trust and guide them to take action that leads to security breaches.
Why and how does social engineering work? Let’s take a closer look.
How social engineering works
Cybercriminals use social engineering to access valuable, sensitive information without complex technology. The main elements of a social engineering attack are:
- Research – criminals gather information about the victim from publicly available resources. This makes it easier to design a successful plan of attack.
- Contact – criminals use the information they gather to contact the target and validate their fake identity.
- Attack – criminals leverage the obtained information (login credentials, credit card numbers) to orchestrate a cyberattack.
Social engineering experts aren’t just hackers. They are usually great psychologists. They understand the person’s needs and feelings and use them to achieve their malicious goals.
Why social engineering works
Social engineering works because it uses human psychology. Instead of investing time and money into complex technological attacks, tricking the victim into serving the data on a silver platter is much easier.
Poor cybersecurity measures
Small and mid-size businesses rarely invest a sufficient amount of time and money into cybersecurity for two reasons:
- Lack of funds
- Lack of awareness
Meanwhile, 46% of all cyberattacks hurt small and medium-sized businesses. Six out of ten small companies that face a cyberattack go out of business within six months.
A closer focus on cybersecurity measures can prevent most social engineering attacks and save company money.
Human kindness and empathy
One of the most effective ways of tricking a person into providing sensitive information is to exploit their kindness and empathy. A popular type of cyberattack called vishing (phishing through phone calls) is an excellent example.
The criminal calls the victim and pretends to be a damsel in distress or a victim’s friend in trouble. Bit by bit, they get the person to share personal information, go online to reveal credit card numbers, and so on.
Human greed and fear
Similar to kindness and empathy, other human emotions can contribute to the success of social engineering. For example, a malicious actor can target a disgruntled ex-employee and trick them into sharing sensitive information to “get back” at the company.
Many business owners don’t pay enough attention to login credentials that ex-employees hold on to. When such a worker leaves the company with little to lose, they are more likely to share information willingly.
To avoid this issue, it’s imperative to review inactive accounts regularly. Ideally, the deactivation of access rights should happen during the offboarding process.
Another popular technique that threat actors use is the Fear Of Missing Out (FOMO). When people are worried that they may miss something if they don’t take immediate action, they become inattentive to detail. This turns such people into perfect targets.
Lack of employee education
Employees often give up sensitive information freely. They also click on malicious links and download all types of malware. The majority of these people don’t have bad intentions. They honestly believe that they aren’t doing anything wrong.
Cybercriminals understand that employees are the weakest link, especially those with high authorization levels. They take a psychological approach to fooling them into taking dangerous steps and sharing information.
Providing proper cybersecurity training to employees can prevent most attacks that depend on social engineering. Additionally, you can review authorization levels and make sure that their distribution matches the real needs of your team.
Social proof
Social proof is a psychological phenomenon that involves people copying the actions of others to choose a course of action for themselves. For example, a person may rely on online reviews to determine which product to buy.
Malicious actors take advantage of this phenomenon to fool victims into sharing information. They fabricate proof that another employee has already shared information or previously used software provided by the criminal. This makes it easy for an employee to agree.
Authority
Every day, most people obey orders because they hope to get rewards or avoid the negative consequences of disobedience. They also obey because they believe that authority is legitimate. Some people are even willing to obey orders to harm others.
Threat actors use the person’s willingness to obey an authority figure to steal sensitive information. They often pose as managers, team leaders, or CEOs to prevent a victim from questioning their “orders.”
Arming yourself against social engineering attacks
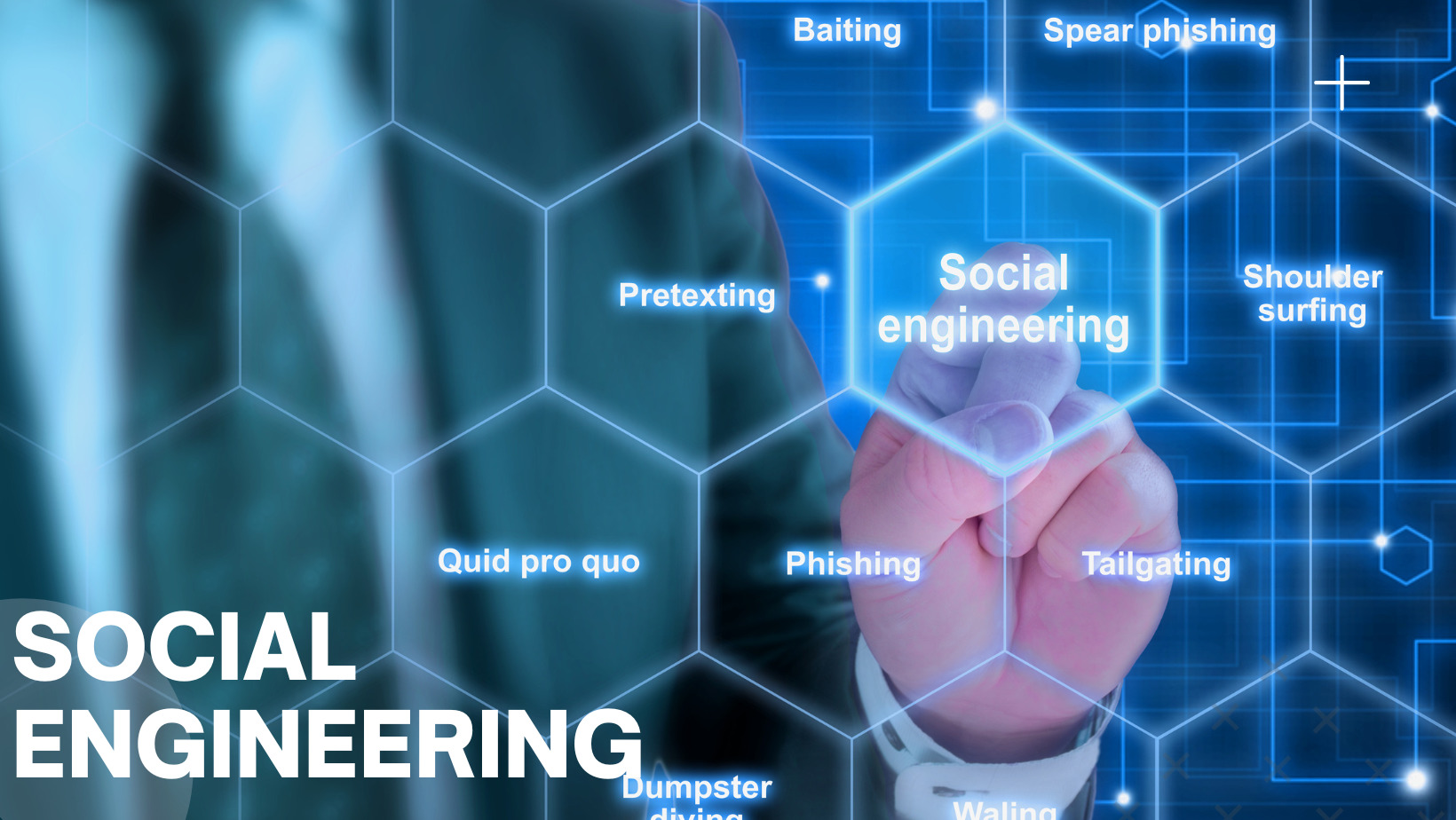
Social engineering is a broad term which encompasses a variety of tactics that malicious actors use to fool the end user into taking action.
No matter how much malicious genius stands behind the attack, it’s possible to eliminate this danger by implementing the right cybersecurity measures. The most effective methods include:
- Using cybersecurity software (firewalls, antivirus, encryption, network security monitoring)
- Implementing authorization tiers
- Removing inactive accounts
- Running phishing drills (simulate an attack to see how they react) for employees
The key to battling social engineering attacks is educating people. The more a person knows about cyberattack methods, the less likely they are to become victims of the scam or put the entire company in danger.




